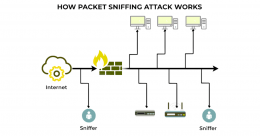
What Is Packet Sniffing in Cyber Security and How to Prevent It?
 By Yashika Aneja . April 24, 2026
By Yashika Aneja . April 24, 2026
The world’s networks transmit billions of data packets every second, with each one bearing fragments of your emails, passwords, financial information, business secrets, and whatnot. That...