Imagine that your team is busy all day, blocking malware warnings and phishing emails. Then a hidden Domain Name System (DNS) request sneaks past that sends you traffic to a malicious website. And the result is system downtime or a data breach, which is a regulatory nightmare for businesses. As the cyber threats grow, traditional security layers like firewalls often struggle to stop threats.
This challenge is growing due to malware, phishing campaigns, and command and control attacks. Now the security teams need smarter techniques to stop threats earlier. Each year, the number of cybercrime reports has been increasing.
The financial losses are valued in billions of Indian rupees annually, and sectors like IT, Healthcare, Finance, and Manufacturing are most vulnerable and leave your in-depth defense strategy full of holes.
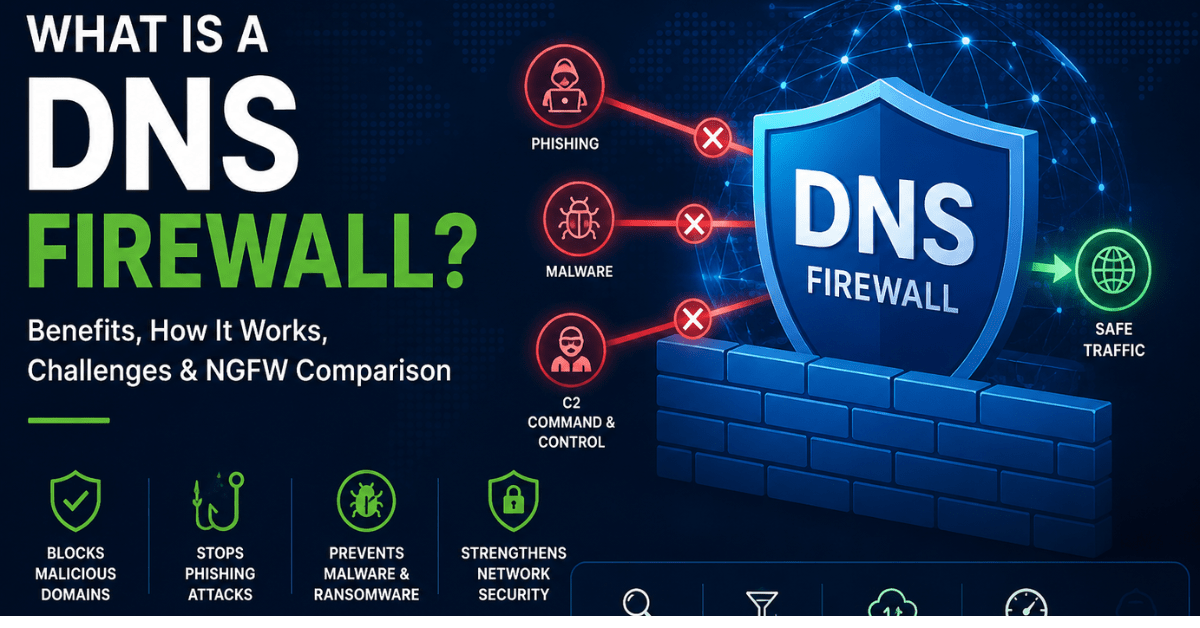
That’s when a DNS firewall comes with a proactive shield that blocks malicious domains and ensures compliance without slowing your network. In this blog post, let’s understand the importance of DNS Firewall and what to consider when choosing the right solution.
A domain name (DNS) firewall provides network security by detecting malware and preventing users and systems from connecting to unauthorized domains, making it an essential cybersecurity solution for modern businesses. It offers proactive insights on potential threats and identifies suspicious activity to prevent malware earlier in the connection chain.
DNS Firewall works by capturing and analyzing DNS queries, and then allows, blocks, or redirects requests based on the security policies. If the firewall detects that a specific traffic violates any rules or policies, then the web requests get blocked. It gets updated automatically with the latest threat data for your business protection against emerging threats.
Now, consider a small business where employees regularly click links in web pages or emails. The company routes all traffic through a DNS firewall that stays between the employee device and the internet to inspect domain lookup.
When a user taps a link, the query is verified against real-time threat information to detect any malicious activity. Then the firewall restricts the access and redirects the user to a safe warning page. This is how it can reduce the likelihood of an attacker launching virtual attacks.
This is a powerful layer in modern network protection that delivers security-centric benefits. Below are the key benefits and challenges that showcase how this layer of protection strengthens security. Along with the visibility, complexity, and policy management that organizations need to tackle challenges.
Prevents DNS Tunneling & Exfiltration
DNS firewalls detect and block DNS tunnelling, an attacker’s way to collect user credentials for mapping out the network and steal sensitive information. DNS tunnelling signs are random-looking subdomains that get flagged or blocked before sensitive information is exfiltrated.
Stops Spear-Phishing Redirect Attacks
This kind of attack tricks user to visit malicious domains, and when a user clicks on it, the DNS security pauses the redirection by blocking the domain. This helps to prevent phishing-based redirects by immediately blocking new campaigns.
Disrupts Ransomware Command and Control (C2) Communication
This command and control (C2) technique is used by attackers to communicate with the compromised device. The firewall blocks the DNS resolution to prevent infected devices from establishing and re-establishing control channels. This stops attackers from gaining persistent access.
Filters Malware & Drive-By Payloads
It stops infections earlier in the attack chain by blocking connections to domains that host malware. Also, DNS filtering is quick, reliable, and transparent, and doesn’t slow down devices.
Non-resolvable domains
This occurs when a DNS query cannot be matched to an IP address, which enables attackers to send large volumes of requests from non-existent domains.
Outdated software/Legacy system
Using it creates vulnerabilities, such as a lack of security updates, which leaves bugs. And legacy devices that can’t be easily updated, which makes them easy targets.
Weak security settings
Improperly configured Access Control Lists (ACLs) can allow unauthorized traffic, and complex firewall changes introduce security loopholes.
Choosing between a DNS Firewall and an NGFW is important to build a layered security strategy. A DNS firewall’s main focus is to block malicious domains at the beginning stage, while a next-generation firewall inspects traffic at the network level.
| Aspect | DNS Firewall | Next-Generation Firewall (NGFW) |
|---|---|---|
| When it Acts | It acts as the first step when a device tries to resolve a domain name. | After the connection is established, traffic flows between endpoints. |
| Visibility Focus | Sees which domains are being requested (who is asking and what they want). | Sees what apps are running, who is using them, and what data is moving. |
| Security Posture | Acts like a domain-name gatekeeper, blocking risky destinations early. | Acts like a traffic inspector, scanning and enforcing rules on live connections. |
| Operational Impact | Lightweight for networks; mainly affects DNS resolution, not data flow. | Higher-touch; can introduce latency or complexity due to deep traffic inspection. |
| Ideal Best-Fit Scenario | Environments where early-stage blocking of phishing, malware, and C2 domains is critical. | Environments needing fine-grained control over apps, users, and encrypted traffic. |
Below are the essential capabilities that help you choose a solution that is scalable and aligns with threat prevention goals.
A DNS firewall prevents users from accessing unauthorized destinations or URLs that are involved in cyberattacks. It reduces data breaches and filters suspicious domain requests. Let’s explore the key threats a DNS firewall can prevent.
Conclusion
After going through the entire blog, you must have understood the importance of DNS firewall, how it works, its major challenges, benefits, and how it helps you find a solution that strengthens your security without disrupting the business processes. Utilizing the right DNS firewall capabilities can help you build the strongest security controls.
If your business is planning to choose the right DNS firewall solution, then you can contact the Techjockey to evaluate your needs and get the software as per your business requirements.
Ever found yourself stuck and staring at performance dashboard that indicates trouble when everything… Read More
If your team spends hours digging through logs or is unable to identify the root… Read More
How prepared is your business network to handle an immediate traffic that seems legitimate, but… Read More
Is your current workflow set up built to handle the modern complexity? If your team… Read More
Mobile communication began with the Short Message Service, better known as SMS. It was a… Read More
Do you think AI is sci-fi? If you’ve used voice assistants, watched recommended shows, or… Read More