WIDS and WIPS in Cybersecurity: How They Protect Wireless Networks?

Wireless networks are present everywhere now like offices, warehouses, hospitals, coffee shops, and even manufacturing floors.
But most security discussions are all around firewalls and endpoint protection; the wireless layer often gets less attention than it deserves.
It is important to note that Wi-Fi networks introduce a whole set of risks that simply don’t exist in wired environments.
- Devices connect invisibly.
- Rogue access points can appear without anyone noticing.
- Employees sometimes plug in their own routers ‘just for convenience,’ and suddenly the company network has a backdoor.
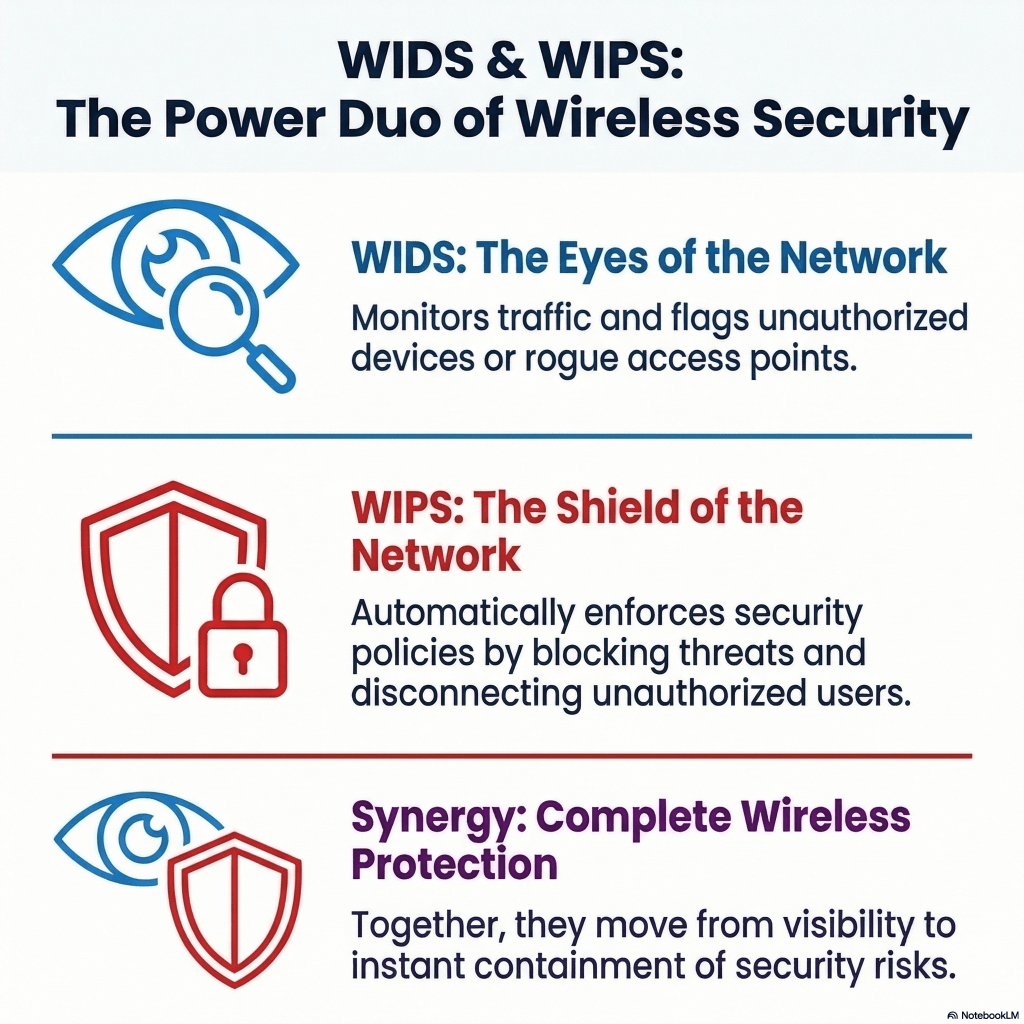
WIDS and WIPS in cybersecurity come together to solve this problem and take care of wireless network security. They monitor Wi-Fi activity, find any suspicious behavior, and help security teams respond to threats.
Let’s break down WIDS and WIPS in practical terms.
What Is a Wireless Intrusion Detection System (WIDS)?
A WIDS, abbreviated as Wireless Intrusion Detection System, is a system that monitors Wi-Fi activity across the complete IT environment. It scans wireless traffic, analyzes the traffic patterns, and alerts administrators whenever it finds something unusual appearing.
However, a WIDS is not made to block anything on its own. It just tells you when something suspicious is happening.
From a security operations standpoint, this is valuable because many wireless threats are surprisingly subtle. Rogue devices don’t always generate obvious alarms. They quietly sit there and wait for someone to connect.
A WIDS helps spot things like:
- Unauthorized or rogue access points
- Unknown devices attempting to connect
- Suspicious authentication attempts
- Evil twin attacks (fake Wi-Fi networks mimicking legitimate ones)
- Misconfigured access points
So, for many security teams, WIDS is like an early warning system. It surfaces activity that would otherwise remain invisible.
According to a report, the average breach now costs organizations over $4.4 million globally. Not every breach comes through wireless networks, obviously, but weak Wi-Fi security is still a surprisingly common entry point, especially in large office setups and campuses. Now, let’s come to the working of WIDS.
How WIDS Works Behind the Scenes?
Technically speaking, WIDS relies on sensors that monitor the radio spectrum used by Wi-Fi devices.
These sensors can be:
- Dedicated wireless monitoring appliances
- Built-in monitoring features within access points
- Software running on network infrastructure
They continuously scan for Wi-Fi traffic and compare it against a known baseline of legitimate devices and access points. When something suspicious appears, the system raises an alert instantly.
For example, A WIDS might see that a new access point suddenly appears using the same network name as the corporate Wi-Fi. That’s a classic sign of an evil twin attack. In this, a fake Wi-Fi network is created by attackers to trick users into connecting.
The WIDS flags it immediately so that a quick decision to fight it could be made.
But as WIDS only reports it, this brings us to the other side of the equation, i.e., WIPS.
What is WIPS in Cybersecurity?
A WIPS, abbreviated as Wireless Intrusion Prevention System, goes one step further. It not only detects wireless threats but also actively prevents or blocks them.
Apart from just sending alerts, the system automatically takes action to protect the network.
Typical WIPS responses include:
- Blocking rogue access points
- Disconnecting unauthorized devices
- Preventing users from connecting to malicious Wi-Fi networks
- Terminating suspicious wireless sessions
For example, imagine someone sets up a rogue access point in a company parking lot and names it after the corporate network. Employees’ laptops might automatically attempt to connect.
In this case, a WIDS would alert administrators. A WIPS, on the other hand, can immediately de-authenticate the connection and prevent the device from communicating with that rogue network. That response happens within seconds, without waiting for a human.
How WIPS Works?
It works in a way that’s similar to WIDS at the beginning, which is constantly scanning wireless traffic across the network using sensors or monitoring access points. The difference between WIDS and WIPS appears after a threat is detected.
In practical terms, a WIPS first analyzes wireless activity and compares it against a database of trusted access points and approved devices. If it detects something outside that list, say an unauthorized access point broadcasting the same SSID as the corporate network, the system immediately responds.
Most WIPS platforms block threats by sending deauthentication packets to disconnect unauthorized devices or prevent them from communicating with the network. Some systems can also quarantine these suspicious attacks or stop employees from connecting to unsafe external Wi-Fi networks.
All of this happens automatically, often within seconds.
From what many network teams observe, speed is the real advantage. Manual intervention is simply too slow when wireless attacks spread quickly. A properly configured WIPS reduces the response time dramatically, sometimes stopping an attack before users even realize something was wrong.
WIDS vs WIPS: Detection vs Prevention in Wireless Security
This comparison highlights the core functional differences between WIDS and WIPS in monitoring and securing Wi-Fi environments.
| Feature | WIDS (Wireless Intrusion Detection System) | WIPS (Wireless Intrusion Prevention System) |
|---|---|---|
| Primary Function | Monitors wireless networks and detects suspicious Wi-Fi activity. | Detects threats and automatically blocks or prevents them. |
| Action Taken | Generates alerts for administrators. | Actively disconnects or blocks malicious devices and networks. |
| Security Approach | Detection-based security monitoring. | Detection plus automated prevention. |
| Response Time | Requires manual investigation and response. | Responds automatically within seconds. |
| Example Threat Handling | Identifies rogue access points or evil twin networks. | Blocks rogue access points and stops devices from connecting. |
| Best Use Case | Visibility into wireless network activity. | Real-time protection against wireless attacks. |
| Deployment Mode | Typically used for monitoring and alerting. | Used for active wireless threat prevention. |
Where WIDS and WIPS Fit in a Real Security Architecture?
Neither technology replaces the other security tools. They complement them.
In a typical enterprise environment, wireless security sits alongside several other layers:
- Network firewalls
- Endpoint detection and response (EDR)
- Network access control (NAC)
- Identity and access management systems
The combination of WIDS and WIPS as Intrusion Detection and Prevention Systems specifically protects the wireless attack surface, which traditional network monitoring tools sometimes miss.
From what most network teams see, wireless threats usually come from three places:
- Rogue internal devices – employees bringing personal routers or hotspots
- External attackers nearby – trying to impersonate networks or intercept traffic
- Misconfigured access points – which unintentionally weaken security
All three are surprisingly common. So, most of the time, WIDS and WIPS are helpful, but there are some instances where both lack. The next section discusses about the loopholes of WIDS and WIPS.
Limitations of WIDS and WIPS in Cybersecurity
Wireless intrusion systems are helpful, but they are not perfect. There are a few practical challenges.
When Safe Devices Get Flagged
Sometimes legitimate devices get flagged as suspicious, especially in large environments with frequent device changes.
Prevention can disrupt users.
Aggressive WIPS policies occasionally disconnect legitimate devices, which frustrates employees.
Gaps Create Risks
If sensors don’t fully cover the building, attackers can operate from blind spots.
From experience, this is where many deployments struggle. Organizations install the technology but underestimate the planning needed for full coverage. Results vary widely depending on the environment. Now, the question comes….
Is it Necessary to Deploy Both WIDS and WIPS?
In modern enterprise networks, the distinction between the two systems is not so visible. Most of the vendors now offer combined WIDS/WIPS platforms.
These solutions provide:
- Continuous monitoring
- Threat detection
- Automated response capabilities
Security teams can choose whether to run them in detection mode or prevention mode, depending on the situation. This hybrid approach tends to work best. You get visibility first, and automation when needed.
Final Thoughts
Wireless networks have quietly become one of the largest attack surfaces in modern organizations. Employees move around with laptops and phones, IoT devices connect automatically, and access points cover entire buildings.
‘That convenience comes with risk.’
Here’s the gist:
A WIDS helps you see what is happening in the wireless environment. It detects rogue devices, suspicious activity, and network anomalies.
A WIPS takes things further by actively blocking those threats before they spread.
Neither solution is perfect on its own, but together they give security teams something that’s surprisingly rare in wireless networks: visibility and control.
And honestly, that’s usually the difference between catching a problem early… and discovering it after the damage is already done.
Mehlika Bathla is a passionate content writer who turns complex tech ideas into simple words. For over 4 years in the tech industry, she has crafted helpful content like technical documentation, user guides, UX content, website content, social media copies, and SEO-driven blogs. She is highly skilled in... Read more