VAPT: Bridging the Gap Between Organizations & their Cyber Security Measures

We live in a world of hyperconnectivity, where huge streams of data are exchanged in less than a second. But with this hyper-connectivity often has the downside of increased cyberattacks. In the past 1 year only, around 95% of executives have reported at least one case of data breach.
Highlighting Cybersecurity Threats
Coronavirus pandemic has further brought to light the dissonance between a business perception and on ground reality of cyberattacks.
Not only this, coronavirus related breaches affected more than 40% of companies by April 2023.
But it seems that business owners have not taken a leaf out of corona’s book yet. 75% business owners admitted that their existing system security policies were not completely aligned with Covid-19 response plans.
If the pandemic continues to run amok, we can only imagine how many companies would be exposed to cyber threats and network compromises.
How are Cybersecurity Threats Posing a Larger Business Risk
Any cyberattack dents your organisation’s reputation. Many businesses find it hard to recover from them with over 60 percent of small enterprises shutting shops within 6 months after falling prey to hacking.
A CNBC report, estimated that cyberattacks are costing companies ₹1,46,66,820 in revenue and resources required to get their system up and running once more.

Frequent cyberattacks harm your company’s reputation and upset the confidence of investors and customers. Already 54% consumers believe that businesses nowadays are not doing enough to protect their data.
And then, there can be legal consequences of data breach too. As per privacy laws, an organisation is bound to safeguard any personal data it records. In case the data gets compromised, the organisation may have to bear fines or sanctions.
Key Takeaways from Cybersecurity Strategies Adopted by Businesses in 2023
Security focused businesses perform better
Business leaders with a proactive approach towards security were able to perform better than those with a relaxed approach by a margin of 50-65 percentage points.
Stronger system security measures = Better Performance
85% of enterprises opting for system security measures were able to track the positive impact on business performance.
Having a BISO helps in countering cyber threats
80% of business aligned security leaders use the services of a business information security officer (BISO) who updates them on latest threats on counter actions. In comparison only 35% non-aligned companies have the position of a BISO.
How to Bring Businesses & Cyber Security Strategies on the Same Page
Around 68 percent of businesses have seen a rise in cyberattacks in the past 2 years and 77 percent expect more data breaches in the coming years.
As technology expands, multiple opening points are being created which can be exploited by hackers to steal important information.
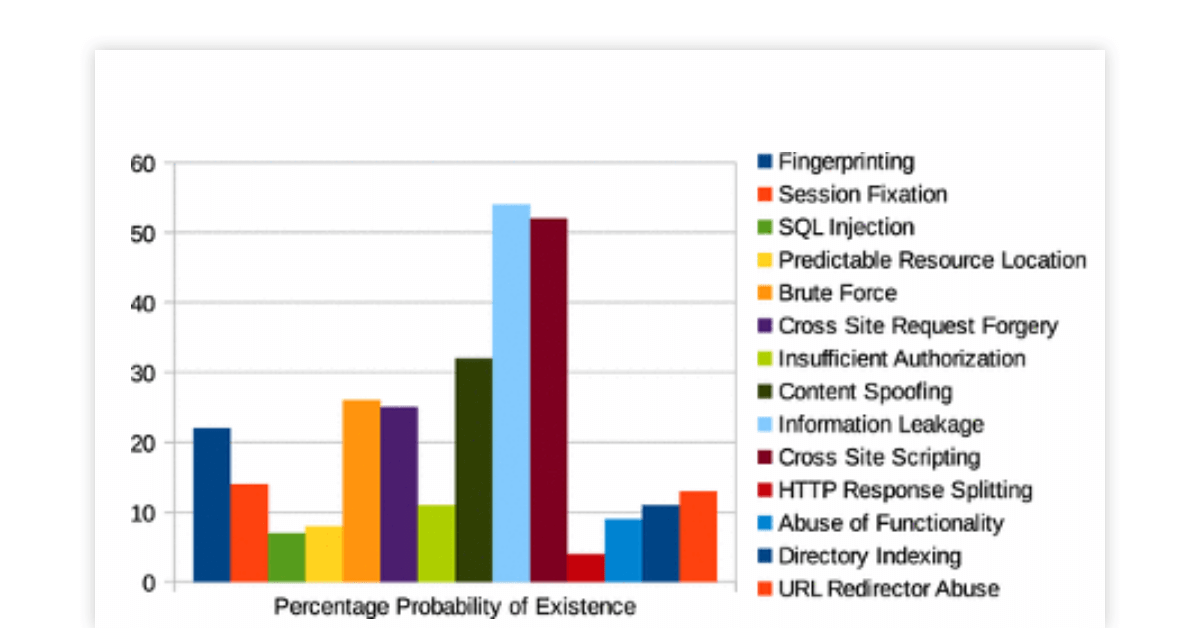
Majorly, there has been a rise in malware, ransomware, DDoS attacks on enterprises. The bottom line is that no matter how many safeguards you implement for your network system, there might be some vulnerability waiting to be exploited.
In such a scenario, a better approach would be to know different vulnerabilities in your system beforehand and rectify them before they can manifest to system crippling incidences.
There exists no better security service than VAPT for this.
VAPT refers to Vulnerability Assessment and Penetration Testing. It is a testing service meant to identify gaps in your security system,and list which security lapses might ultimately lead to business losses.
How Does VAPT Provide Business-Risk Context to Security Leaders
A staggering 36 percent business owners depicted their cybersecurity policy as being reactive, i.e. focussed more on handling risks on day to day basis rather than having a long-term approach. For such businesses, VAPT offers the required context in risks to their system
VAPT consists of two parts: Vulnerability Assessment (VA) and Penetration Testing (PT). VA focuses on bringing all sorts of vulnerabilities to the fore and is meant for internal data of the company. PT, on the other hand, identifies which threats can comprise security and is directed towards external data.
VA and PT combine to benefit organisations in the following manner-
- VAPT has both an automated and manual approach to conduct searches with large and small scope to identify all gaps existing within your system
- By implementing VAPT, organisations can obtain risk factors associated with their critical assets including operational technology assets, IoT etc.
- Through VAPT, businesses can put remediation measures as per priority so that vulnerabilities posing the maximum risk are rectified first. This is useful for small businesses with a tight budget and limited availability of cybersecurity experts
- VAPT assessments are conducted frequently on different parameters. Reports detailing risks and solution for their mitigation are shared with stakeholders
Suggested Read: Top Managed Security Service Providers (MSSP) in India
Smart Cyber Security Investments with VAPT: Need of the Hour
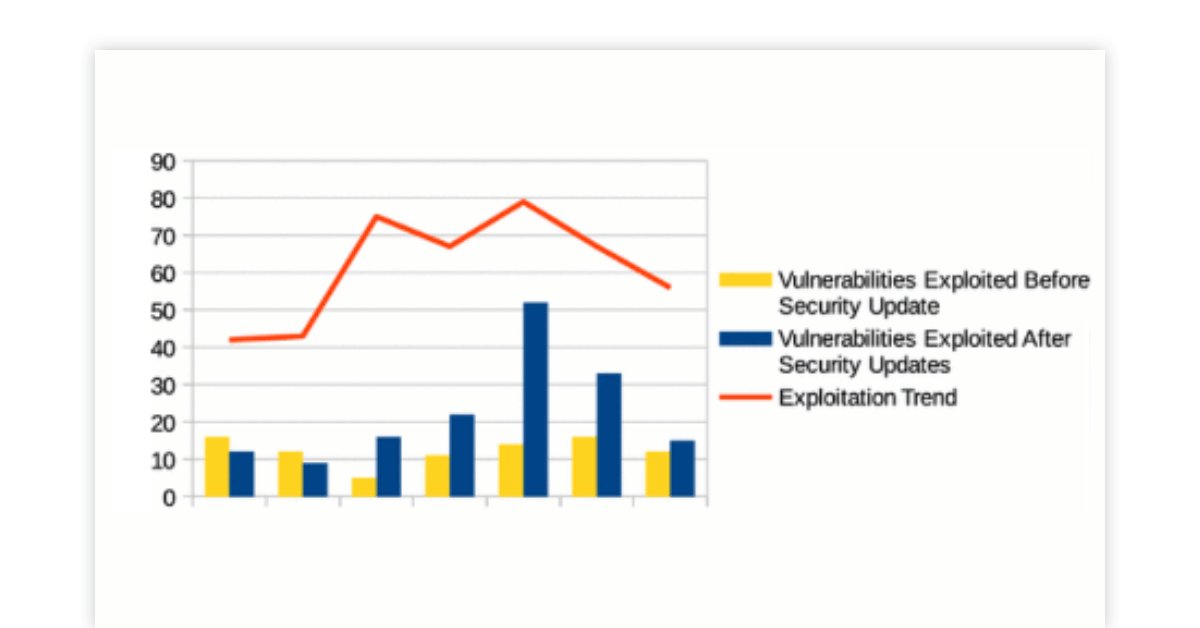
VAPT is a helpful tool for businesses to align their cybersecurity policy with their growth strategies. It also enables business leaders to take a proactive approach towards data breach rather than a reactionary approach.
By investing in VAPT, you can even conduct threat perception, i.e. evaluation of possible threats in present and future threats, on an automated basis and as per your business’s needs. Vulnerability Assessment and Penetration Testing analyses both internal data and external data from clients and vendors for all possible pain points.
In addition, VAPT nudges your security team in the right direction as it builds a blueprint for how, when and where to analyse risks.
We at Techjockey provide VAPT service to several businesses for safeguarding their systems with the firm belief that prevention is far better than the reactive approach. A cyberattack can put brakes on your progress and it takes tremendous time and effort to get back up.
That’s why we suggest that today is the right time to empower your network protection. Use VAPT to adopt an attacking stance on cyberthreats and bring your business goals in consonance with your system security policy.
Mayank Dixit is a talented content writer with an enriching educational background with Bachelor's degree in Engineering and a Master's degree in Mass Communication. With this combination of technical and creative skills, Mayank is well-equipped to produce engaging content that is informative too. He is passionate about business... Read more