What Is a DoS Attack in Cyber Security? Definition, Types, and Prevention
If you spend enough time around IT teams or security engineers, you must have heard the phrase ‘Denial of service attack’. Usually, after a website suddenly slows down, or worse, stops responding completely.
It might sound technical and complex, but it’s surprisingly simple to understand. Someone deliberately overwhelms a system that even the real users can’t access it.
Just give it a thought!
There is a small restaurant that offers its services to 40 customers per hour. Now, if 5,000 people come suddenly and block the entrance, not to eat, but just for fun, the customers who actually came to eat will not be able to enter the restaurant. The restaurant technically still exists, but it might as well be closed.
That, in essence, is the denial of service meaning in cybersecurity.
Of course, in the digital world, the methods are more sophisticated, and the scale can be enormous.
In the field of cybersecurity, modern DoS attacks have brought down government portals, banking applications, game systems, and even major cloud providers. And in case you operate a site, a SaaS, or an API infrastructure, YOU COULD BE THE NEXT TARGET.
To defend yourself, it is necessary for you to learn what a Denial of Service attack is and how to prevent it. So, we can start with its simple understanding.

Azure DDoS Protection
Starting Price
Price on Request
What is a Denial of Service (DoS) Attack?
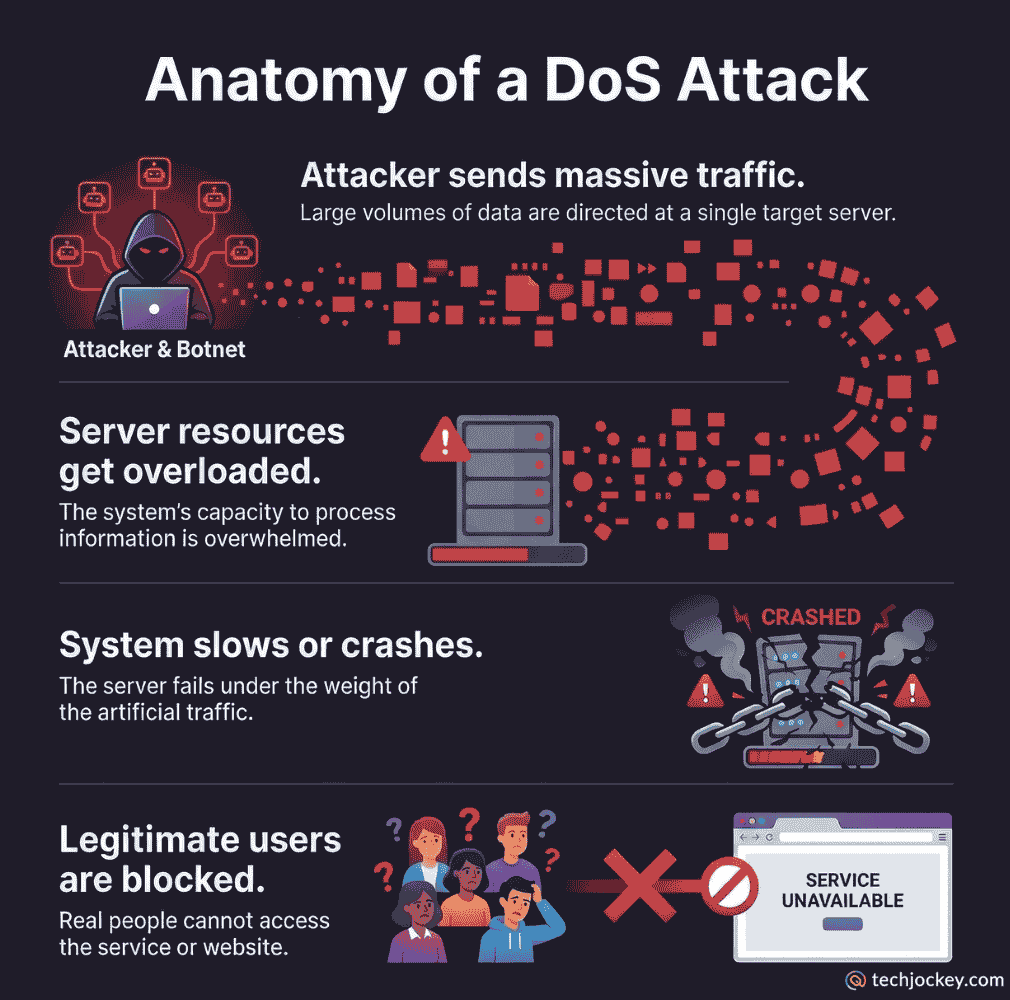
A denial of Service (DoS) attack is a type of cyber attack that may make a website, a server, or a network inaccessible to its real users.
The question is, how does the attacker do this?
They overload the target system with huge traffic, requests, or data packets. The resources of the system, such as CPU, memory, bandwidth, or application threads, eventually get exhausted. When that occurs, the system just breaks down.
That is why the DoS attack in computer security is frequently referred to as a resource exhaustion attack. The hacker does not always need to crack into the system. They overpack it instead, until it fails under pressure.
- In practice, there are multiple consequences depending on the target.
- A small business website might go offline for hours.
- A financial service platform could lose transactions and user trust.
In some cases, attacks are used as distractions while other breaches happen quietly in the background.
It is reported by a security firm that DoS and DDoS attacks increased by more than 30% in a single year. It is largely because automated attack tools have become easier to access. Unfortunately, that trend hasn’t slowed down.

Radware DefensePro
Starting Price
Price on Request
DoS vs DDoS: A Quick Clarification
While discussing denial of service attacks, people often mention DDoS attacks as well.
They are closely related, but not identical.
A DoS attack usually originates from a single machine or network source.
A Distributed Denial of Service (DDoS) attack uses thousands, or even millions of compromised devices to launch the attack simultaneously.
These devices often belong to regular users whose computers, routers, or IoT devices were infected with malware.
The infamous Mirai botnet attack in 2016 is a good example. It used hundreds of thousands of hijacked devices to flood DNS provider Dyn. It temporarily disrupted major services like Netflix and Twitter.
From what most security teams see today, DDoS attacks are far more common than traditional DoS attacks. And it’s mainly because botnets are widely available in underground markets.
Common Types of DoS Attacks
Not all types of DoS attacks work the same way. Attackers target different layers of a system depending on the infrastructure and vulnerabilities involved.
Here are several Denial of Service attack types commonly encountered in cybersecurity environments.
1. Volumetric Attacks
These attacks aim to consume all available bandwidth between the target and the internet. The attacker floods the network with massive traffic, often measured in gigabits or terabits per second.
Common examples include:
- UDP floods
- ICMP floods
- DNS amplification attacks
In these scenarios, the network pipe simply gets saturated. Even if the servers are healthy, legitimate traffic cannot reach them.
Large organizations sometimes use cloud-based traffic scrubbing services to fight against this attack, though even those systems occasionally struggle during extremely large attacks.
2. Protocol Attacks
Protocol attacks exploit weaknesses in network protocols such as TCP or ICMP.
One well-known example is the SYN flood attack.
Here’s what happens:
- The attacker sends thousands of TCP connection requests.
- The server responds with acknowledgment packets.
- The attacker never completes the handshake.
The server keeps waiting for responses that never arrive. Over time, its connection queue becomes full. When that happens, real users can’t connect to the server. This attack doesn’t need a lot of bandwidth; it simply takes advantage of how network communication protocols work.

Radware DefenseFlow
Starting Price
Price on Request
3. Application Layer Attacks
Application-layer attacks are often harder to detect because they look like normal user behavior. They do not overwhelm the network; attackers target specific parts of a web application.
Examples include:
- HTTP request floods
- Login request abuse
- Search query flooding
These attacks can be surprisingly effective. A complex database query executed thousands of times per second can quickly exhaust server resources.
From experience, this is where many organizations get caught off guard. Traditional firewalls might allow the traffic because it appears legitimate.
4. Slow Rate Attacks
Some Denial of Service attack types don’t rely on high traffic volume at all. They send extremely slow or incomplete requests that keep server connections open for long periods.
One well-known example is the Slowloris attack.
The attacker opens many connections but sends data very slowly, preventing the server from closing them. Over time, the server runs out of available connection slots.
These attacks are subtle and often difficult to identify without proper cybersecurity tools.
Why Do Attackers Launch DoS Attacks?
People sometimes assume every DoS attack in cybersecurity is politically motivated or part of cyber warfare. That does happen, but many attacks are far more mundane.
Common motives include:
- Financial extortion: Attackers threaten to bring down a service unless a ransom is paid.
- Competitive sabotage: This occurs occasionally in industries like online gaming, betting platforms, or e-commerce.
- Hacktivism: Groups target organizations to protest political or social issues.
- Distraction for larger breaches: Security teams have noticed that DoS attacks sometimes occur alongside other intrusion attempts.
Warning Signs of a DoS Attack
In many cases, denial of service attacks don’t appear instantly catastrophic. The early signs are often the same as some ordinary performance issues.
You might notice things like:
- Sudden increasing network traffic
- Website responding slowly
- Increased server CPU usage
- Unusual traffic from a single IP range
- Frequent service timeouts
In real operations environments, teams often discover attacks by noticing unusual patterns in traffic logs rather than dramatic system failures. Sometimes it takes a few minutes or longer to confirm what’s actually happening.
How to Prevent a Denial of Service Attack?
No system can be made completely immune to Denial of service attacks. That’s an uncomfortable truth most security professionals will admit.
However, the goal is to make attacks harder, slower, and less effective. Several practical strategies help reduce the risk.
1. Use Traffic Filtering and Rate Limiting
Rate limiting is used to limit the number of requests that a particular user or IP address can send within a given time. In case of a sudden flood of requests by one source to a system, the server can block that traffic.
Large numbers of modern web gateways and API management software have in-built rate-limiting features.
2. Deploy Web Application Firewalls
The Web Application Firewall (WAF) is positioned between the customer and the server. It examines traffic coming in and blocks possible suspicious traffic before it enters the application. WAFs are especially applicable in identifying attacks at application-layer such as HTTP floods.
However, they aren’t perfect. Complex attacks even imitate legitimate user activity.

Thales Application Security
Starting Price
Price on Request
3. Use Content Delivery Networks (CDNs)
Content Delivery Networks distribute the web traffic to numerous servers that are in various locations. In case a server is overloaded, the load may be shared among other nodes. This will greatly enhance the resilience in the event of high traffic bursts. A lot of large websites use CDNs as a secondary means of dealing with DoS and DDoS traffic.
4. Network Monitoring and Early Detection
Continuous monitoring helps identify abnormal traffic patterns before they escalate.
Security teams typically track:
- Traffic spikes
- Protocol anomalies
- Geographic traffic distribution
- Request patterns
Early detection can sometimes allow teams to reroute traffic or apply defensive rules before systems fail.
5. Cloud-Based DDoS Protection Services
Large-scale attacks often require specialized protection services offered by cloud providers. These services use large traffic filtering infrastructures to absorb and analyze incoming traffic.
While they are not cheap, many organizations consider them essential for protecting mission-critical applications.
Why DoS Attacks Continue to Grow?
Despite improvements in security technology, denial of service attacks in cybersecurity continue to increase.
There are a few reasons for this.
- First, attack tools have become easier to access. Even individuals with limited technical knowledge can launch basic attacks using prebuilt scripts or rented botnets.
- Second, the internet itself has expanded dramatically. The number of connected devices, especially IoT devices, has created millions of potential targets for botnet recruitment.
- Security researchers often estimate that tens of billions of connected devices now exist globally, many of which have weak security configurations. That creates a massive pool of devices that attackers can exploit.
- And finally, businesses rely more heavily on online services than ever before. When a platform goes offline today, the consequences are immediate.
Final Thoughts
Businesses are greatly affected due to a denial of service attack. When systems go down, customers lose access, and operations become slower, which highly affects customers’ trust.
While tools like traffic filtering, CDNs, rate limiting, and monitoring help reduce the risk, no defense is fully guaranteed.
The best approach is layered security and good visibility into system activity. The faster an attack is detected, the easier it is to limit damage.
And… prevention is always better than the cure…
Since online services are essential for businesses, DoS attacks will likely remain a constant cybersecurity challenge. So, you must think about building resilient systems that can handle pressure and keep running even during an attack.
And this is how you can prevent yourself from being a target of not only denial-of-service attacks but of every type of cybersecurity attack.
Mehlika Bathla is a passionate content writer who turns complex tech ideas into simple words. For over 4 years in the tech industry, she has crafted helpful content like technical documentation, user guides, UX content, website content, social media copies, and SEO-driven blogs. She is highly skilled in... Read more