Get Quote
Looking for pricing details or customization options?
Share your requirements and receive a tailored quote
Price Available on Request
Get a customized quotation based on your needs.
Our team will respond within 24 hours.
We make it happen! Get your hands on the best solution based on your needs.
Have recommended this product
Overall Score
Review this product
Your valuable feedback helps others like you make a better decision.
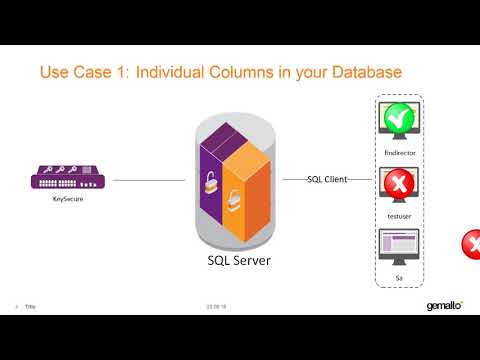
| Brand Name | Gemalto |
| Information | Gemalto |
| Founded Year | 2006 |
| Director/Founders | Axalto Holding N.V |
| Company Size | 1000+ |
| Other Products | Gemalto SafeNet KeySecure K460, Gemalto SafeNet Tokenization, Gemalto SafeNet ProtectApp, SafeNet Luna Payment HSM |



















20,000+ Software Listed
Best Price Guaranteed
Free Expert Consultation
2M+ Happy Customers