Get Quote
Get Quote

We make it happen! Get your hands on the best solution based on your needs.

Endpoint Security
It offers comprehensive protection for devices against cyber threats, ensuring the security of sensitive data.
Clientless Connectivity
It enables secure access to corporate resources without requiring additional software installations.
VPN Remote Access
It facilitates secure remote access to corporate networks through encrypted VPN connections.
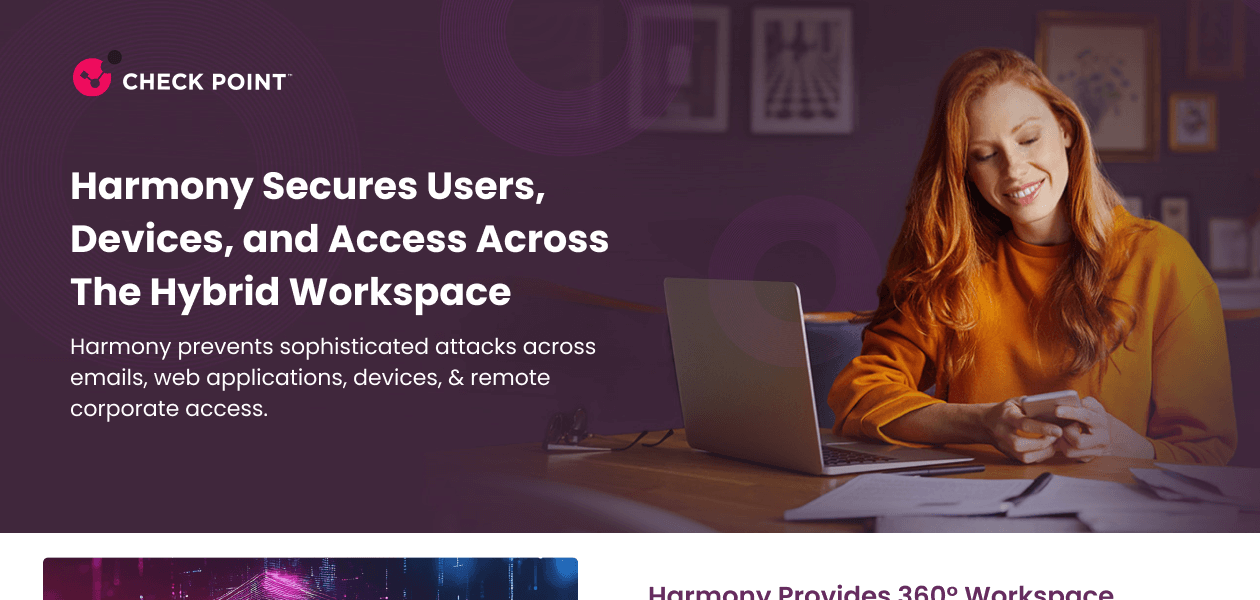
Email Security
It provides robust protection against phishing attacks, malware, and spam to safeguard organizations' email communications.
Secure Internet Browsing
It ensures secure browsing by blocking malicious websites and preventing drive-by downloads.
Workforce Security Report
It generates detailed reports on endpoint security status, compliance levels, and potential risks for informed decision-making.
Have recommended this product
Overall Score
Review this product
Your valuable feedback helps others like you make a better decision.
Pros
“Robust cybersecurity features; seamless integration with existing IT infrastructure; proactive threat intelligence updates.” Tahsin Ahemad - Jul 3, 2025
“Robust threat detection; seamless Nano Agent integration; minimal performance impact.” Suheb - Jun 12, 2025
“Zero-day threat prevention; ransomware rollback capabilities; detailed forensics.” Sushil Kukreti - May 12, 2025
Cons
“Integration issues with certain third-party applications; occasional data synchronization problems.” Tahsin Ahemad - Jul 3, 2025
“URL filtering could be improved; limited customization options.” Suheb - Jun 12, 2025
“High resource consumption; limited compatibility with newer operating systems.” Sushil Kukreti - May 12, 2025
| Brand Name | Check Point Software Technologies |
| Information | Check Point Software Technologies Ltd. Checkpoint is a leading provider of cyber security solutions to governments and corporate enterprises globally. Its solutions protect customers from 5th generation cyber-attacks with an industry-leading catch rate of malware, ransomware and other types. |
| Founded Year | 1993 |
| Director/Founders | Gil Shwed |
| Company Size | 1000+ Employees |
| Other Products | Check Point Sandblast, Check Point Endpoint Security, Perimeter 81, Next Generation Security Management Software, SandBlast TE Appliance TE100X |



















20,000+ Software Listed
Best Price Guaranteed
Free Expert Consultation
2M+ Happy Customers