Get Quote

Looking for pricing details or customization options?
Share your requirements and receive a tailored quote
Price Available on Request
Get a customized quotation based on your needs.
Our team will respond within 24 hours.
We make it happen! Get your hands on the best solution based on your needs.

Have recommended this product
Overall Score
Review this product
Your valuable feedback helps others like you make a better decision.
Pros
“Robust cybersecurity features; seamless integration with existing IT infrastructure; proactive threat intelligence updates.” Tahsin Ahemad - Jul 3, 2025
“Robust threat detection; seamless Nano Agent integration; minimal performance impact.” Suheb - Jun 12, 2025
“Zero-day threat prevention; ransomware rollback capabilities; detailed forensics.” Sushil Kukreti - May 12, 2025
Cons
“Integration issues with certain third-party applications; occasional data synchronization problems.” Tahsin Ahemad - Jul 3, 2025
“URL filtering could be improved; limited customization options.” Suheb - Jun 12, 2025
“High resource consumption; limited compatibility with newer operating systems.” Sushil Kukreti - May 12, 2025
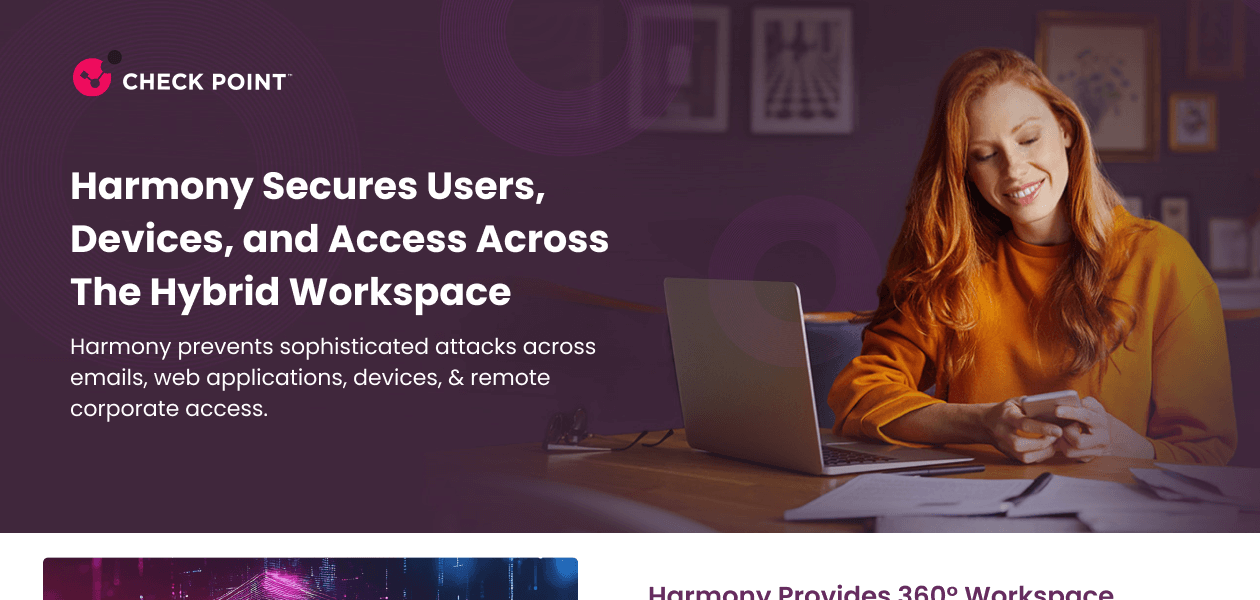
| Brand Name | Check Point Software Technologies |
| Information | Check Point Software Technologies Ltd. Checkpoint is a leading provider of cyber security solutions to governments and corporate enterprises globally. Its solutions protect customers from 5th generation cyber-attacks with an industry-leading catch rate of malware, ransomware and other types. |
| Founded Year | 1993 |
| Director/Founders | Gil Shwed |
| Company Size | 1000+ Employees |
| Other Products | Check Point Sandblast, Check Point Endpoint Security, Perimeter 81, Next Generation Security Management Software, SandBlast TE Appliance TE100X |



















20,000+ Software Listed
Best Price Guaranteed
Free Expert Consultation
2M+ Happy Customers