In today's digital world, cyber security is no longer an option, it's a necessity. Cyberattacks are becoming increasingly sophisticated and prevalent, posing a significant threat to businesses, organizations, and individuals alike. These attacks can result in data breaches, financial losses, reputational damage, and even downtime, disrupting operations and impeding business continuity.
Organizations understand the importance of safeguarding their sensitive information and infrastructure from cyber threats. Cybersecurity software plays a crucial role in protecting against unauthorized access, data breaches, and other potential threats. This document aims to provide a comprehensive guide to help organizations make informed decisions when choosing and implementing cyber security software.
The Ever - Growing Threat Landscape
According to the Astra Security reports, cyber attacks occur on a daily basis, with around 2, 200 happening each day. Shockingly, a cyber attack occurs every 39 seconds on average. In the United States, the cost of a data breach averages $ 9.44 million. Experts also predict that by 2023, cybercrime will cost a staggering $8 trillion.
What is Cyber Security Software?
Cyber security software refers to a set of technologies, tools, and applications designed to safeguard digital assets and prevent unauthorized access. It encompasses a wide range of functionalities, including intrusion detection, firewalls, antivirus software, encryption, and more.
By implementing robust cyber security measures, organizations can mitigate risks and protect their sensitive data, systems, and networks against cyberattacks. This software can be used to protect against a variety of threats, including:
- Malware
- Phishing attacks
- Ransomware
- Data breaches
The Role of Cyber Security Software
Cybersecurity software serves as a critical defense against these evolving threats.It encompasses a range of tools and technologies designed to protect networks, systems, and data from unauthorized access, modification, or destruction. This software plays a vital role in safeguarding sensitive information, preventing financial fraud, and ensuring business continuity.
Types of Cyber Security Software
The cyber security software landscape is diverse, offering a variety of solutions to address specific threats and vulnerabilities. Some of the most common types of cybersecurity software include:
- Antivirus and Anti-Malware Software: These programs detect and neutralize malicious software, such as viruses, worms, and Trojan horses, that can harm systems and compromise data.
- Firewall Software: Firewalls act as gatekeepers, monitoring and controlling network traffic to block unauthorized access and prevent malicious actors from infiltrating systems.
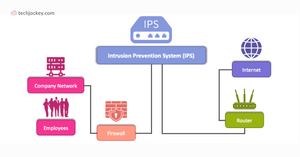
- Intrusion Detection and Prevention Systems(IDS / IPS): IDS / IPS systems continuously monitor network activity for suspicious behavior and take action to prevent attacks before they can cause damage.
- Data Loss Prevention(DLP) Software: DLP software aims to prevent sensitive data from leaving an organization's premises, whether through accidental or malicious means.
- Endpoint Security Software: Endpoint security solutions protect individual devices, such as laptops and smartphones, from malware, phishing attacks, and unauthorized access.
- Network Security: Prevents unauthorized access to networks through firewalls, intrusion detection systems, and access control lists.
- Data Encryption: Ensures the protection of sensitive data by encrypting it, making it difficult for unauthorized individuals to access or tamper with it.
- Web Filtering: Controls and manages access to websites, blocking malicious or inappropriate content to safeguard employee productivity and network integrity.
- Web Application Security: Provides security for web applications and APIs, identifying and mitigating vulnerabilities to prevent data breaches and unauthorized access.
- Continuous Monitoring and Alerting: Automates security monitoring, alerting the organization to potential breaches, incidents, or security events in real-time.
- Security Awareness Training and Education: Educates employees about best security practices, phishing scams, and other cyber threats to enhance their awareness and reduce the risk of security breaches.
Features of the Best Security Software
There are many kinds of security software, each with its own set of features. However, most security software provides these essential features to ensure complete cybersecurity:
- Real-Time Scanning: Security software helps in scanning every email attachment and link to protect the company from malicious attacks.
- Multi-App Protection: Every application, whether it’s a business email, internet browser, or instant messenger, everything is protected by internet security software. Also, you can control access to different applications, based on pre-defined roles.
- Remediate Incidents Effectively: The best security software ensures immediate remediation, as soon as a threat is detected. This way, malware can be cured effectively with higher threat visibility.
- Single Sign-On: Users can access multiple applications by logging in name and password once at a single place. This is applicable to authorized users only.
- Incident Response Approach: The incident response approach can be set with computer security software, which is critical for organizations to encounter and eliminate threats instantly.
- Multi-Tenant Security: Different users can assess the same application, however, their case to data will vary. Only those who are authorized to access the data can do so.
- Device and Operating System Protection: The current trend has moved from BYOD to CYOD, that is, from Bring Your Own Device to Choose Your Own Device. Employees are now bringing different devices, which use different operating systems. So, you need free security software that ensures complete device protection, operating in different operating systems.
- Continuous Detection: A robust endpoint security software helps with the continuous detection of malware, viruses and other cyber threats. Thus, preventing the company’s data and network from falling into the wrong hands.
Benefits of Cyber Security Software
There are many benefits to using cybersecurity software. These benefits include:
- Protection against cyberattacks: Cyber security software can help to protect your data and systems from cyberattacks.
- Compliance and Regulatory Requirements: Many industries, such as finance and healthcare, have strict regulatory requirements regarding data protection. Cybersecurity software helps organizations meet these requirements and maintain compliance.
- Enhanced Data Privacy: Data encryption and secure access controls ensure that sensitive data remains confidential and protected from unauthorized access.
- Employee Productivity: By protecting systems and networks from malware and unauthorized access, organizations can reduce the risk of disruptions and downtime, enhancing employee productivity and efficiency.
- Customer Trust and Confidence: Implementing strong security measures demonstrates a commitment to data protection, fostering trust and confidence among customers, clients, and other stakeholders.
- Data protection: Cyber security software can help to protect your data from unauthorized access, disclosure, alteration, or destruction.
Factors to Consider When Choosing Cyber Security Software
Selecting the right cyber security software requires careful consideration of various factors:
- Threat Assessment: Identify the types of cyberattacks your organization is most vulnerable to, such as ransomware, phishing, or data breaches.
- Relevant Certifications: Look for software that has relevant industry certifications, such as ISO 27001 or NIST, to ensure the software meets industry standards and regulatory requirements.
- Budgetary Constraints: Cybersecurity software pricing can vary significantly. Set a realistic budget that aligns with your organization's financial capacity.
- Organizational Size and Complexity: Consider the size and complexity of your IT infrastructure, ensuring the chosen software can effectively protect your network and systems.
- Ease of Use and Scalability: Evaluate the user interface and scalability of the software to accommodate future business growth and evolving security needs.
- IT Compatibility: Assess compatibility with your existing IT infrastructure, ensuring seamless integration and minimizing disruption.
- Support and Maintenance: Evaluate the vendor's support and maintenance offerings, including the availability of technical assistance, regular software updates, and incident response capabilities.
Cyber Security Software Statistics
- The global cyber security market is expected to grow at a CAGR of 10.9 % from 2021 to 2028, reaching a value of $ 345.4 billion by 2028.
- The North American cyber security market is valued at $ 45.4 billion in 2021, accounting for the largest market share worldwide.
- Europe holds the second-largest market share, valued at $ 36.9 billion in 2021.
- Asia Pacific is the fastest-growing region, with a CAGR of 13.2 % from 2021 to 2028.
Conclusion
Cyber security software protects organizations from the ever-evolving cyber threat landscape. Organizations can safeguard their valuable data, maintain business continuity, and protect their reputation by carefully assessing risks, setting a realistic budget, and selecting the appropriate software.